What are AI SOC Services?
AI SOC (Security Operations Center) services use modern AI models, traditional machine learning, and automation to improve threat detection, investigation, and response. These solutions move beyond manual rules to proactively hunt threats, reduce alert fatigue, automate triage and response, provide deeper insights, and deliver 24/7 coverage cost-effectively.
Key capabilities and functions include:
- Automated threat detection and triage: AI sifts through massive data, spots subtle patterns, filters false positives, and prioritizes real threats, reducing manual work.
- Accelerated incident response: Automates investigations, correlates data across sources, and prepares detailed incident reports with root causes and response plans for faster action.
- 24/7 coverage: AI agents provide tireless, autonomous monitoring, solving staffing gaps and ensuring threats are addressed off-hours.
- Contextual intelligence: Learns from organizational data (policies, past incidents) for context-aware responses, providing a full incident story.
- Proactive defense: Uses predictive analytics to identify vulnerabilities before exploitation, shifting from reactive to proactive security.
- Analyst augmentation: Frees human analysts from repetitive tasks to focus on complex, strategic decisions, improving overall team productivity.
This is part of a series of articles about SOC services
Key Capabilities and Functions of AI SOC Services
Automated Threat Detection and Triage
AI SOC services scan vast quantities of data for anomalies or signs of compromise without the need for constant human oversight. Machine learning algorithms analyze user behaviors, network traffic, and system logs to identify patterns that could represent threats. These systems can correlate data from multiple sources, reducing false positives by focusing on genuinely suspicious activity.
Once a potential threat is detected, the AI engine can automatically triage alerts based on severity, context, and potential business impact. This triage process ensures that only the most relevant, actionable events are escalated to human analysts. By automating detection and triage, organizations can significantly reduce alert fatigue, allowing security teams to concentrate on investigating and remediating real incidents, not wasting valuable time on benign or duplicate notifications.
Accelerated Incident Response
When threats are detected, AI SOC services can guide or automate a large portion of the incident response process. These services offer playbooks and automated workflows that orchestrate tasks such as isolating compromised systems, blocking malicious IPs, or collecting forensic evidence across environments. This decreases the mean time to respond (MTTR), limiting the window of opportunity for attackers.
Moreover, AI-driven incident response improves consistency by ensuring that each step follows predetermined best practices, reducing the risk of manual errors or oversight. The system can also learn from previous incidents, adapting response playbooks to new attack methods. As a result, organizations not only respond faster but also improve over time, creating a continuously strengthened security posture.
24/7 Coverage
Unlike human analysts bound by shifts and work schedules, AI SOC services offer continuous monitoring around the clock. These platforms operate non-stop, analyzing incoming threats and data streams without fatigue or lapse in concentration. This constant vigilance ensures that security incidents can be identified and acted upon immediately, regardless of the time of day or the geographic location of the threat.
Around-the-clock coverage is vital, as attackers often exploit weekends, holidays, or late nights when human teams are less active. With AI SOC services, organizations eliminate gaps in monitoring, reduce detection delays, and build resilience against adversaries who rely on timing their attacks for maximum impact.
Contextual Intelligence
AI SOCs employ advanced data enrichment and correlation methods to provide deep context around each alert or incident. These systems combine information from internal sources—such as endpoint logs, user activity, and cloud APIs—with external intelligence feeds, vulnerability databases, and threat actors’ tactics. This results in richer, more actionable insights for security teams.
With contextual awareness, alerts generated are not just raw data points but findings with attached relevance, urgency, and suggested response actions. This context helps analysts prioritize incidents effectively, understand potential attack paths, and make informed decisions quickly. In turn, this reduces investigation time and enhances the quality of incident handling.
Proactive Defense
AI SOC services are not limited to reacting to threats; they also focus on anticipating and preventing attacks before they materialize. By analyzing historical and real-time data, these systems identify emerging trends or weak spots in the environment, enabling security teams to take pre-emptive measures. Some platforms run continuous threat hunting tasks, scanning for indicators of compromise or vulnerabilities that attackers might exploit.
Proactive defense also includes recommending or automatically initiating mitigation actions, such as tightening access controls, patching vulnerable systems, or simulating attacks to test defenses. This approach shifts cybersecurity from a reactive stance to one of anticipation and continuous improvement, making it harder for adversaries to succeed.
Analyst Augmentation
AI SOC services augment security analysts, not just automate basic tasks. These platforms provide decision support, real-time investigation assistance, and advanced analytics that help human teams move faster and with more confidence. Features may include natural language query interfaces, case recommendations, and automated reporting.
By offloading repetitive or data-heavy processes to AI, analysts are empowered to focus on complex investigations or higher-value initiatives. The result is a more effective and motivated SOC team, capable of managing more incidents without burnout, and driving continuous enhancements to the organization’s security strategy.
Benefits of AI SOC Services
Improved Efficiency
AI SOC services bring automation to tasks that previously required extensive human effort, such as correlating alerts, triaging incidents, or generating compliance reports. Automation streamlines workflows, processes voluminous security data at scale, and shortens timeframes for detecting and responding to threats. This means fewer delays in identifying risks and acting upon them, directly improving incident management cycles.
Reduced Costs
The adoption of AI SOC solutions can significantly lower the costs associated with maintaining an in-house 24/7 security operations center. Automated platforms decrease the need for large, highly specialized teams by handling routine monitoring and initial investigations. This staffing efficiency reduces overhead while providing the same, or even improved, coverage and accuracy that larger manual SOC teams deliver.
Enhanced Security Posture
Leveraging AI-driven security operations strengthens an organization’s overall cyber defense posture through improved visibility, agility, and adaptation. AI SOCs minimize blind spots by continuously analyzing streams of data from across the enterprise, correlating findings for a holistic view of risks. This comprehensive monitoring makes it harder for threats to slip through unnoticed.
Notable AI SOC Services
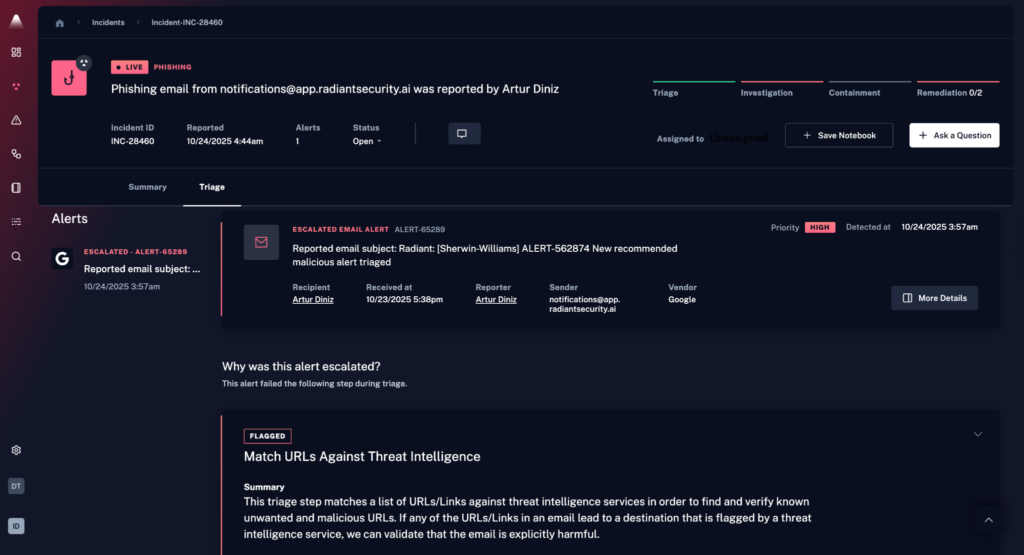
1. Radiant Security
Radiant Security is an Agentic AI SOC platform that automates alert triage, investigation, and response across the security lifecycle. The platform is designed to reduce false positives by roughly 90%, enabling analysts to spend more time on verified threats rather than manual triage. Radiant also aims to shorten investigation and response times (MTTR) and lower operational costs, while helping teams avoid the fatigue that often comes with high alert volume.
Key capabilities include:
- Agentic AI triage and investigation for all alert types, including previously unseen or low-fidelity ones.
- Transparent reasoning that shows how and why the AI reached its conclusions, helping analysts validate decisions and build trust.
- Integrated response with one-click, executable action plans that can be carried out manually or automated when appropriate.
- Log management with unlimited retention, delivered at a cost significantly lower than traditional SIEM platforms.
- AI feedback loop that allows teams to influence and adjust triage behavior using environmental context, improving accuracy over time.
Radiant provides a unified environment for handling alerts, investigations, response actions, and log data, with an emphasis on efficiency, clarity, and analyst control.
2. Stellar Cyber
Stellar Cyber offers an AI-powered SOC platform built around an open extended detection and response (Open XDR) architecture. It automates data collection, analysis, and correlation across the full attack surface, including network, endpoints, cloud, and applications. The solution integrates and reduces security data into a unified, enriched format called Interflow™, helping teams detect real threats faster and trace them to root causes.
Key features include:
- Open XDR integration: Consolidates data from network, internet, and cloud sources into a single, actionable view
- Interflow technology: Correlates events into enriched, high-context records for faster root-cause analysis
- Automated threat detection: Uses machine learning to reduce false positives and improve detection over time
- Visual kill chain interface: Guides analysts through alert investigation and response with intuitive workflows
- Broad data collection engine: Gathers the right data across all infrastructure layers without manual tuning
3. Google Security Operations
Google Security Operations (SecOps) is a cloud-native platform that combines SIEM, SOAR, and threat intelligence into a unified experience designed to modernize security operations. Built on Google’s infrastructure, it delivers scalable ingestion, detection, and response with the speed and context needed to keep up with today’s evolving threats. The platform integrates curated detections with advanced automation and AI-powered tools.
Key features include:
- Curated and custom detections: Built-in, continuously updated detection rules from Google’s threat researchers, plus support for custom rules using YARA-L
- Generative AI assistance: Use Gemini to search telemetry, create detections, generate summaries, and investigate cases with natural language
- Streamlined data management: Route, transform, and enrich security telemetry through advanced pipeline controls for better data readiness
- Context-rich investigation: Automatic correlation and stitching of entities, interactive alert graphs, and a threat-centric case interface
- Fast, flexible search: Perform real-time, context-aware searches across security data to support investigations
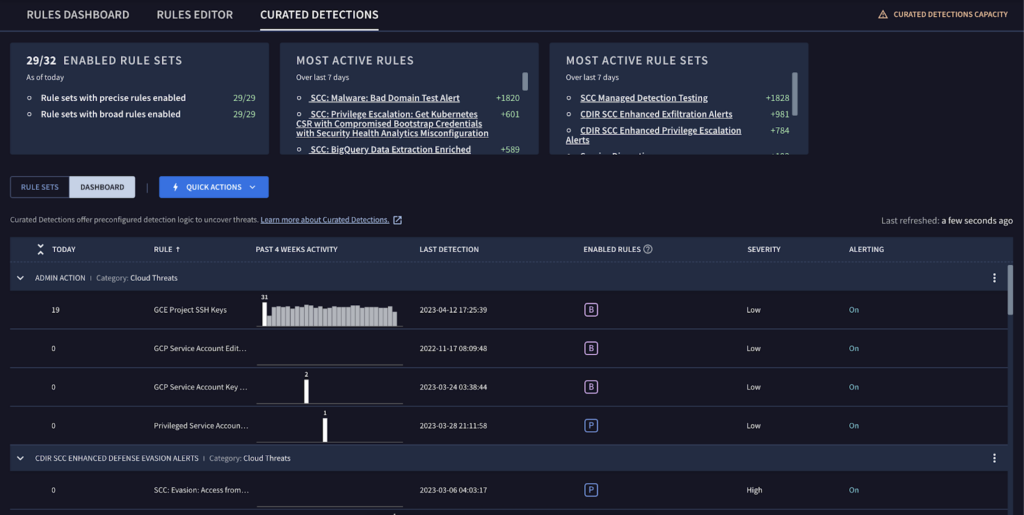
Source: Google Security Ops
4. Prophet Security
Prophet Security offers an AI SOC platform built around an agentic model that transforms how teams triage, investigate, and respond to alerts. Designed to tackle alert fatigue, slow investigations, and failed automation efforts, Prophet acts as an autonomous SOC analyst that significantly reduces manual workloads. It cuts investigation time by up to 90% while improving analyst efficiency and helping security teams focus on high-value threats rather than repetitive tasks.
Key features include:
- Automated triage planning: Instantly summarizes alerts and builds adaptive investigation plans without analyst input
- Autonomous investigation: Emulates human analysts by retrieving and correlating security data across systems to uncover root causes
- Intelligent response actions: Prioritizes alerts, determines severity, and delivers remediation steps directly into existing workflows
- Continuous learning: Improves over time by learning from analyst decisions and tuning actions to match the organization’s context
- Efficiency gains: Reduces time spent on low-value alerts and repetitive tasks, freeing analysts for strategic investigations
5. Dropzone AI
Dropzone AI delivers AI SOC analysts designed to replicate the investigative techniques of elite human analysts without fatigue or delay. Designed for Tier 1 triage and alert investigation, Dropzone AI autonomously handles every incoming alert with speed, depth, and transparency. It integrates easily into existing environments, delivering operational value rapidly..
Key features include:
- Autonomous alert investigation: Replicates expert analyst workflows to triage and fully investigate every alert, start to finish
- Detailed, transparent reports: Delivers clear, evidence-backed findings so analysts understand and trust the AI’s output
- Day-one value: Deploys in minutes with minimal configuration and delivers immediate operational impact
- Human-in-the-loop design: Follows analyst instructions, supports custom workflows, and continuously learns from feedback
- Scalable Tier 1 support: Adds virtual analyst capacity without hiring, enabling the team to handle any alert volume
Source: DropZone AI
Conclusion
AI SOC services have matured into essential tools for modern security teams, offering capabilities that extend far beyond traditional rule-based systems. By combining automation, contextual intelligence, and always-on monitoring, they enable faster, smarter, and more scalable security operations. Whether used to supplement existing SOC teams or to replace them in leaner organizations, these platforms deliver measurable gains in efficiency, cost reduction, and threat coverage.

